cybersecurity - Network
The Weird Way A DEC Alpha Boots
https://poliverso.org/display/04...
We’re used to there being an array of high-end microprocessor architectures, and it’s likely that many of us will have sat in front of machines running x86, ARM, or even PowerPC processors. There are other players past and present you may be familiar with, for example SPARC, RISC-V, or MIPS. Back in the 1990s there was another, now long gone but at the time the most powerful of them all, of course we’re speaking of DEC’s Alpha architecture. [JP] has a mid-90s AlphaStation that doesn’t work, and as part of debugging it we’re treated to a description of its unusual boot procedure.
Conventionally, an x86 PC has a ROM at a particular place in its address range, and when it starts, it executes from the start of that range. The Alpha is a little different, on start-up it needs some code from a ROM which configures it and sets up its address space. This is applied as a 1-bit serial stream, and like many things DEC, it’s a little unusual. This code lives in a conventional ROM chip with 8 data lines, and each of those lines contains a separate program selectable by a jumper. It’s a handy way of providing a set of diagnostics at the lowest level, but even with that discovery the weirdness isn’t quite over. We’re treated to a run-down of DEC Alpha code encoding, and should you have one of these machines, there’s all the code you need.
The Alpha was so special in the 1990s because with 64-bit and retargetable microcode in its architecture it was significantly faster than its competitors. From memory it could be had with DEC Tru64 UNIX, Microsoft Windows NT, or VMS, and with the last of which it was the upgrade path for VAX minicomputers. It faded away in the takeover by Compaq and subsequently HP, and we are probably the poorer for it. We look forward to seeing more about this particular workstation, should it come back to life.
hackaday.com/2025/04/03/the-we…
3.4.2025 23:00The Weird Way A DEC Alpha Bootshttps://poliverso.org/display/04...
*Lynx ransomware: come il gruppo criminale sta svuotando le casse delle aziende USA*
https://poliverso.org/display/04...Lynx ransomware: come il gruppo criminale sta svuotando le casse delle aziende USA
@Informatica (Italy e non Italy 😁)
Il mondo del ransomware non conosce tregua, e ogni anno, ogni mese emergono nuove minacce più sofisticate e aggressive. Tra le ultime varianti che stanno facendo tremare le aziende statunitensi c’è Lynx, un ransomware che, sin dalla sua comparsa
https://poliverso.org/display/04...
Teardown of a Scam Ultrasonic Cleaner
https://poliverso.org/display/04...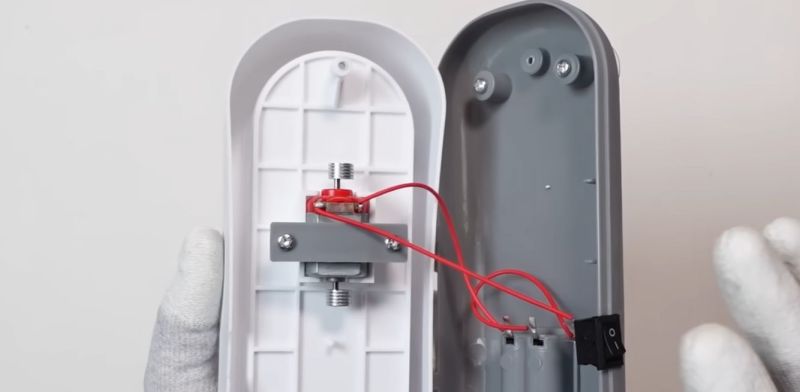
Everyone knows that ultrasonic cleaners are great, but not every device that’s marketed as an ultrasonic cleaner is necessarily such a device. In a recent video on the Cheap & Cheerful YouTube channel the difference is explored, starting with a teardown of a fake one. The first hint comes with the use of the description ‘Multifunction cleaner’ on the packaging, and the second in the form of it being powered by two AAA batteries.
Unsurprisingly, inside you find not the ultrasonic transducer that you’d expect to find in an actual ultrasonic cleaner, but rather a vibration motor. In the demonstration prior to the teardown you can see that although the device makes a similar annoying buzzing noise, it’s very different. Subsequently the video looks at a small ultrasonic cleaner and compares the two.
Among the obvious differences are that the ultrasonic cleaner is made out of metal and AC-powered, and does a much better job at cleaning things like rusty parts. The annoying thing is that although the cleaners with a vibration motor will also clean things, they rely on agitating the water in a far less aggressive way than the ultrasonic cleaner, so marketing them as something which they’re not is very unpleasant.
In the video the argument is also made that you do not want to clean PCBs with an ultrasonic cleaner, but we think that people here may have different views on that aspect.
youtube.com/embed/GUmaT2IhUJo?…
hackaday.com/2025/04/03/teardo…
3.4.2025 20:00Teardown of a Scam Ultrasonic Cleanerhttps://poliverso.org/display/04...
Australia’s Silliac Computer
https://poliverso.org/display/04...
When you think about the dawn of modern computers, you often think about the work done in the UK and the US. But Australia had an early computer scene, too, and [State of Electronics] has done a series of videos about the history of computers down under. The latest episode talks about SILLIAC, a computer similar to ILLIAC built for the University of Sydney in the late 1950s. How many racks does your computer fill up? SILLIAC had quite a few.
How many racks does your computer fill up? SILLIAC had quite a few.
This episode joins earlier episodes about CSIRAC, and WREDAC. The series starts with the CSIR Mark I, which was the first computer in the southern hemisphere.
The -AC computers have a long history. While you often hear statements like, “…in the old days, a computer like this would fill a room,” SILLIAC, in fact, filled three rooms. The three meters of cabinets were in one room, the power supply in another. The third room? Air conditioning. A lot of tubes (valves, in Australia at the time) generate a lot of heat.
It is hard to put an exact cost on SILLIAC, but the original estimate was about AU£35,200. That sounds modest, but at the time, you could buy about ten suburban homes near Sydney for that price. Like most projects, the cost rose, and completion depended on a larger donation from a horse race. At the end, the cost was about AU£75,000!
SILLIAC had a reputation of being more reliable than some other computers based on the same design. That was probably because most computers use 6J6 tubes, but SILLIAC used 2C51 devices. Bell Labs created the 2C51 for use in undersea cables. Of course, they were also about six times the cost of a 6J6.
The computer did important work until 1968. It was, sadly, dismantled, but pieces of it are hanging around the Powerhouse Museum and at the University as display items.
This series is a great look at what was happening in the computer world south of the equator during these days. While SILLIAC is fascinating, you might want to start with episode 1. Supercomputers have come a long way.
youtube.com/embed/tJdB3QZpVKA?…
hackaday.com/2025/04/03/austra…
3.4.2025 18:30Australia’s Silliac Computerhttps://poliverso.org/display/04...
*I 10 migliori password manager: cosa sono, come usarli e perché sono utili anche alle aziende*
https://poliverso.org/display/04...I 10 migliori password manager: cosa sono, come usarli e perché sono utili anche alle aziende
@Informatica (Italy e non Italy 😁)
Questi programmi e app che archiviano in modo sicuro e crittografato le credenziali (username e password) hanno vantaggi e svantaggi. Vediamo come usarli, perché e quali sono i migliori
L'articolo I 10 migliori password manager: cosa
https://poliverso.org/display/04...
Ditto That
https://poliverso.org/display/04... All the news that was fit to print. Image via Wikipedia
All the news that was fit to print. Image via Wikipedia
In the 1982 movie Fast Times At Ridgemont High, a classroom of students receives a set of paperwork to pass backward. Nearly every student in the room takes a big whiff of their sheet before setting it down. If you know, you know, I guess, but if you don’t, keep reading.
Those often purple-inked papers were fresh from the ditto machine, or spirit duplicator. Legend has it that not only did they smell good when they were still wet, inhaling the volatile organic compounds within would make the sniffer just a little bit lightheaded. But the spirit duplicator didn’t use ghosts, it used either methanol (wood alcohol), isopropyl, or, if you were loaded, ethyl alcohol.
Invented in 1923 by Wilhelm Ritzerfeld, ditto machines were popular among schools, churches, and clubs for making copies of worksheets, fliers, and so on before the modern copy machine became widespread in the 1980s. Other early duplicating machines include the mimeograph, the hectograph, and the cyclostyle.
Getting A Handle On Duplication
To use the ditto machine, one would first make a master copy using a special sheet of paper with a special type of waxy ink on the back that dissolves in alcohol. These types of sheets are still around today, in a way — if you’ve ever gotten a tattoo, you know that they don’t usually just freehand it; the artist will draw out your design on special paper that they can then use to lay down a temporary tattoo on your freshly-shaved skin before going for it. Image via Wikipedia
Image via Wikipedia
But don’t get too excited; tattoo transfer sheets aren’t compatible with ditto machines for a number of reasons. As I mentioned, ditto sheets use alcohol to transfer the ink, and tattoo sheets use heat and pressure. They’re too thin for the mechanics of the ditto machine’s drum, anyway.
So once you’ve typed or drawn up your master sheet, you’d mount it on the drum of the ditto machine. Then, with a big crank handle, you’d roll the drum over sheet after sheet until you had what you needed. The average master could make roughly 50 to 500 copies depending a number of factors.
The rise of higher-quality master sheets is largely responsible for this wide range, but there are other factors at play, like the color that gets used. Purple was made from a dye called aniline purple and lasted longest on paper, although there was also green, red, and black. You see a lot of purple dittos because of its vibrancy and the fact that it was highly soluble in alcohol.
The type of paper entered into the equation as well: absorbent paper like newsprint would make fewer copies than smoother, less porous bond paper. And, as you might imagine, dense text and images used more ink and would wear out the master faster.
youtube.com/embed/ccYLLzpeVnU?…
As with many paper-based things from decades ago, the durability of dittoes is not so great. They will fade gradually when exposed to UV light. Although there is no citation, Wikipedia claims that the average ditto would fade in direct sunlight after about a month. It goes on to assume that most ditto machine users printed onto low-quality paper and will eventually “yellow and degrade due to residual acid in the untreated pulp”.
Not a Mimeograph
It’s worth mentioning that mimeographs are not quite the same thing as ditto machines. For one thing, ditto machines were often hand cranked, and many mimeographs were motorized. Interestingly enough, the mimeograph predates the spirit duplicator, having been patented on August 8, 1876 by Thomas Edison and popularized by the A.B. Dick Company in the 1880s.
Also known as stencil duplicators, mimeographs were a competing technology that used ink and stencils to produce 50 to several thousand copies. A special stencil sheet bearing a wax coating would be typed on a regular typewriter with the ribbon disengaged and the machine set to this mode, and/or written or drawn upon using a special stylus and lettering guides.
The stencil sheet would then be fed into the machine, which had a large drum with an ink pad. The mimeograph would then squish ink through the stencil and onto the paper. You can see all this and more in the video below, which illustrates just how much of an art this whole process was compared to makin’ copies today.
youtube.com/embed/gYjj62eGwc8?…
Mimeographs were largely done in black, but color could be done “easily”, as the video demonstrates. You basically had to hand paint the colors onto your stencil. It doesn’t seem as though changing out the giant ink pad was an option. Unlike dittoes, mimeographs required better paper, so they should last longer in theory.
Before You Run Off
Duplication for the common man is as important as the printing press itself. While today you might just set the printer to provide the number of copies you need, the history of duplication shows that we’ve come a long way in terms of effort on the user’s end. Keep this in mind the next time you want to go Office Space on it.
hackaday.com/2025/04/03/ditto-…
3.4.2025 17:00Ditto Thathttps://poliverso.org/display/04...
*VPN aziendali: proteggere e connettere le aziende*
https://poliverso.org/display/04...VPN aziendali: proteggere e connettere le aziende
@Informatica (Italy e non Italy 😁)
Le VPN aziendali garantiscono connessioni sicure e crittografate, proteggendo i dati sensibili e migliorando la flessibilità operativa. Grazie alla loro capacità di ridurre i rischi informatici e assicurare la conformità alle normative, rappresentano una soluzione indispensabile per il lavoro
https://poliverso.org/display/04...
*Sicurezza dell’identità macchina a prova di futuro: ecco la tabella di marcia*
https://poliverso.org/display/04...Sicurezza dell’identità macchina a prova di futuro: ecco la tabella di marcia
@Informatica (Italy e non Italy 😁)
La sicurezza dell’identità macchina è oggi fondamentale per una solida strategia di sicurezza aziendale, attuabile concentrandosi su gestione centralizzata, automazione, cripto-agilità e preparazione al quantum computing. Ecco come iniziare
https://poliverso.org/display/04...
MIT Wants You to Secure Your Hardware Designs
https://poliverso.org/display/04...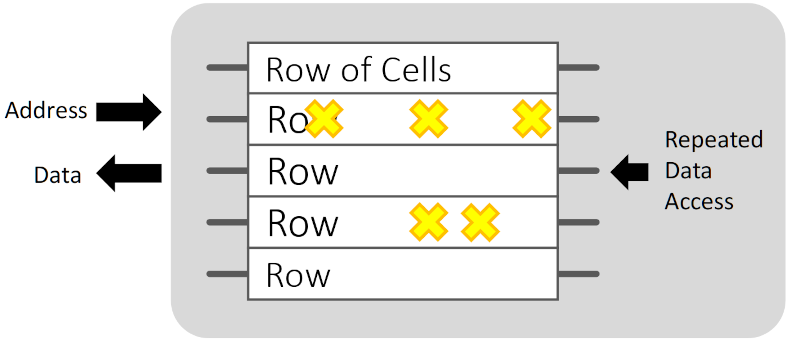
When you think of attacking or defending computer systems, you probably think of software viruses and the corresponding anti-virus software. But MIT’s 6.5950 class teaches secure hardware design — how to attack and defend CPUs from bad actors. Interested? The course is open source, so you can follow along as long as you don’t mind not getting a grade.
Browsing some of the lecture slides shows that the material isn’t as stuffy as you might imagine. A slide about side channel attacks, for example, features an article called “And Bomb the Anchovies,” which says that Washington DC pizza places know when big news is about to break because pizza delivery to places like the White House or the Pentagon trend upward (something spies call pizza-int, by the way).
Even if you don’t have a burning desire to design more secure hardware, some of the lecture slides make for an interesting flip through on a rainy weekend day. For example, the charts about RowHammer (“RowHammer in One Sentence”) is a great explanation about how software can cause DRAM failures to attack a computer. We only wished they’d identified companies A, B, and C in their study. There are also labs and they politely clarify what setup you need to do each lab (typically, just a Linux server, although some you can do with just a browser).
One of the great things about the Internet is that you can virtually audit classes from anywhere in the world, often for free. MIT is always up to something interesting.
hackaday.com/2025/04/03/mit-wa…
3.4.2025 15:30MIT Wants You to Secure Your Hardware Designshttps://poliverso.org/display/04...
Scandalo VPN: Alcune App sull’Apple Store erano legate alla sorveglianza del governo cinese!
https://poliverso.org/display/04...Sono stati scoperti nell’App Store di Apple cinque servizi VPN collegati a strutture militari cinesi. Ciò è stato rivelato come risultato di una indagine congiunta del Tech Transparency Project con il Financial Times. Secondo gli analisti, le app sono sviluppate da aziende legate a Qihoo 360, un colosso informatico cinese che nel 2020 è stato colpito dalle sanzioni statunitensi per i suoi legami con l’esercito cinese.
I servizi VPN si propongono come strumenti per la protezione della privacy su Internet. Permettono, ad esempio, di nascondere l’attività di rete ai provider Internet e di crittografare il traffico durante la connessione a reti pubbliche. Tuttavia, la sicurezza di tali applicazioni dipende direttamente dall’affidabilità dei loro sviluppatori. Se un’azienda raccoglie i dati degli utenti, una VPN può diventare uno strumento di sorveglianza.
Secondo il rapporto, l’elenco delle applicazioni discutibili includeva Turbo VPN, VPN Proxy Master, Thunder VPN, Snap VPN e Signal Secure VPN (non correlato a Signal Messenger). Tre di questi (Turbo VPN, VPN Proxy Master e Thunder VPN) sono stati installati complessivamente più di un milione di volte. Le aziende dietro questi prodotti sono strettamente collegate a Qihoo 360. Inoltre, è stato rivelato che una delle sussidiarie degli sviluppatori, Guangzhou Lianchuang, sta attivamente cercando specialisti con conoscenza della cultura americana per analizzare i dati degli utenti.
A seguito dell’appello dei giornalisti del Financial Times, Apple ha rimosso due app dall’App Store: Thunder VPN e Snap VPN. Il destino degli altri resta incerto. Allo stesso tempo, Apple ha dichiarato di monitorare rigorosamente la conformità delle applicazioni VPN alle sue policy e di rimuoverle immediatamente dallo store alla minima discrepanza.
Qihoo 360, formalmente nota come 360 Security Technology, è presente nell’elenco delle aziende affiliate all’esercito cinese stilato dal Dipartimento della Difesa degli Stati Uniti. Sebbene i proprietari formali delle app siano registrati presso entità giuridiche diverse, l’indagine ha stabilito il loro collegamento con Qihoo attraverso una rete di società e sviluppatori affiliati.
Gli esperti sottolineano che utilizzare servizi VPN sotto la giurisdizione cinese può essere pericoloso, poiché la legge cinese impone agli sviluppatori di conservare i registri degli utenti e di fornirli su richiesta delle autorità. È per questo motivo che nel 2017 Apple ha già effettuato una pulizia su larga scala dell’App Store, rimuovendo tutti i servizi VPN che non rispettavano questi standard.
La situazione attuale solleva interrogativi non solo sulla trasparenza degli sviluppatori, ma anche sulla qualità della revisione delle app sulle piattaforme Apple e Google. Nonostante le misure di sicurezza dichiarate, i servizi inaffidabili continuano a raccogliere milioni di installazioni.
Non è ancora noto se Apple adotterà ulteriori misure sulle app rimanenti. Nel frattempo, si ricorda agli utenti che una VPN affidabile non dovrebbe solo dichiarare di essere sicura, ma anche essere verificata in modo indipendente.
L'articolo Scandalo VPN: Alcune App sull’Apple Store erano legate alla sorveglianza del governo cinese! proviene da il blog della sicurezza informatica.
3.4.2025 14:55Scandalo VPN: Alcune App sull’Apple Store erano legate alla sorveglianza del governo cinese!https://poliverso.org/display/04...